Overview
Registering your computer is as easy as opening a web browser and entering your eID and password.
The purpose of this system is to ensure that all computers connected to the University network meet the minimum security requirements before being granted access.
Who can use this Service?
How can I get this Service?
The registration process will differ depending on the type of computer you are using:
- Windows computers joined to the JMUAD domain
- After the initial registration via web browser, Windows computers joined to the JMUAD domain will automatically register on the network upon logging in to the computer. No further action is required.
- Mac (Apple) computers and non-domain joined computers
- Mac users and non-domain joined computers will manually register every 30 days. Simply open a web browser and enter your eID and password.
Where can I get Help/Support?
Information Technology Help Desk at (540) 568-3555, IT Service Portal or helpdesk@jmu.edu
FAQs
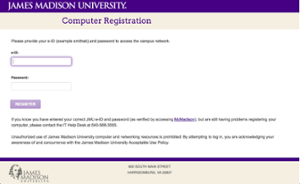
When I open a web browser, what will the registration page look like?
You will be presented with this page, on which you can enter your credentials:
Will I notice anything different when I log in to my computer?
Windows 10 users will notice a slightly different looking Windows login screen containing a picture of a key, and the messages "Windows will try to connect to the network" and "Connecting to the network" after logging in.

Do I have to register my computer when connecting wirelessly or when off campus?
No. Registration is only for wired computers connecting to the on-campus University network.
Are there any indications that my computer is not registered?
Any applications that rely on a network/Internet connection would likely have connectivity issues if a computer were not registered. A common example of this would be a Microsoft Outlook client not being able to connect to the JMU email server. In this case, you may receive a variety of errors when attempting to open Outlook and would be unable to send/receive email messages. Registering the computer (by opening a browser and entering your eID and password) will allow Outlook (and other applications) to connect normally again.
What about student computers in the on-campus resident halls?
Student computers in on-campus resident halls are handled through a different system (MyResNet).
I have an Apple computer that is joined to the JMU Active Directory Domain (JMUAD), why do I need to register every 30 days?
A Group Policy (GPO) has been created for Windows machines, however the Apple operating system does not have the same ability for Group Policy.
