Assessing Perceptions of Group Work Using Team-Based Learning
Lauren Ferry, Phillip J. Wong, and Kathryn Hogan
Psychology
Group work is frequently incorporated into courses; however, student perceptions regarding group work might differ based on the structure of the course. This study used pre- and post-semester surveys to examine perceptions of group work in a team-based learning (TBL) course. While the small sample size leaves room to examine individuals’ different experiences more closely, students' rsponses to closed- and open-ended questions suggest that the TBL structure ensures individual accountability and provides a space for students to practice transferable skills.
"When I Wore a Younger Man's Clothes": The Nostalgia Topic in the Music of Billy Joel
Kendall Waters
Music
My father and I often listened to Billy Joel together as I grew up, and I eventually formed nostalgic connections to Joel’s music. While music is known as a conductor of nostalgia, this paper explores the idea that the nostalgia I feel while listening to specific songs in Joel’s catalog is not simply a result of indexical connections I have built with these tracks. Rather, it is a result of a “nostalgia topic” in Joel’s work. This paper compares select works from Joel’s catalog to reveal that there is no one gesture, melody, or harmonic progression that Joel relies on to create these connections. Instead, Joel amasses a collection of differing musical elements from his nostalgic soundtrack that he then places into the care of the piano.
Parallel Greedy Triangulation of a Point Set
Eliza Shoemaker and Randy Shoemaker
Computer Science
A greedy triangulation algorithm takes a set of points in the plane and returns a triangulation of the point set. The triangulation is built by adding the smallest line segment between points that does not intersect any line previously in the triangulation. The greedy triangulation is inexpensive computationally and gives an approximation of the minimum-weight triangulation problem, an NP-hard problem, which is computationally expensive. We present serial and parallel implementations of the greedy triangulation using the following approach: once a line is added to the triangulation, all intersecting lines are removed from consideration. This process is repeated until a triangulation is obtained. We present and analyze experimental wall-time data for the serial and parallel implementations to show that the parallel version has strong and weak scaling properties, and that this algorithm benefits greatly from parallelism.
The Danger of Apathy: College Students' Receipt of Mumps Vaccine During an Outbreak
Laura A. Keane
Health Sciences
A mumps outbreak occurred on the James Madison University campus during the Spring 2018 semester. For many students, it was the first time they had to decide on their own whether to receive a vaccine. This explanatory, cross-sectional study examined the relationships between students’ general vaccine acceptance; measles, mumps, and rubella (MMR) vaccine acceptance; vaccine knowledge; and intent to receive/receipt of the MMR booster. A survey was distributed in Fall 2019 to students in two health courses. For students enrolled during the Spring 2018 semester, the survey evaluated perceptions and behaviors regarding the MMR vaccine; for those not enrolled in Spring 2018, the survey evaluated perceptions of a hypothetical outbreak. While the surveyed population as a whole had a positive attitude towards vaccines, attitude alone is not enough to persuade an individual to receive a vaccine. More efforts are needed to increase the perceived importance of vaccinations and perceived susceptibility to the consequences of not getting vaccinated.
Deep Fakes: The Algorithms That Create and Detect Them and the National Security Risks They Pose
Nick Dunard
Intelligence Analysis
The dissemination of deep fakes for nefarious purposes poses significant national security risks to the United States. Deep fakes are images and videos created by or with the assistance of AI algorithms in which a person’s likeness, actions, or words have been replaced by someone else’s to deceive an audience. Often created with the help of generative adversarial networks, deep fakes can be used to blackmail, harass, exploit, and intimidate individuals and businesses; in large-scale disinformation campaigns, they can incite political tensions around the world and within the U.S. Their broader implication is a deepening challenge to truth in public discourse. The U.S. government, independent researchers, and private companies must collaborate to improve the effectiveness and generalizability of detection methods that can stop the spread of deep fakes.
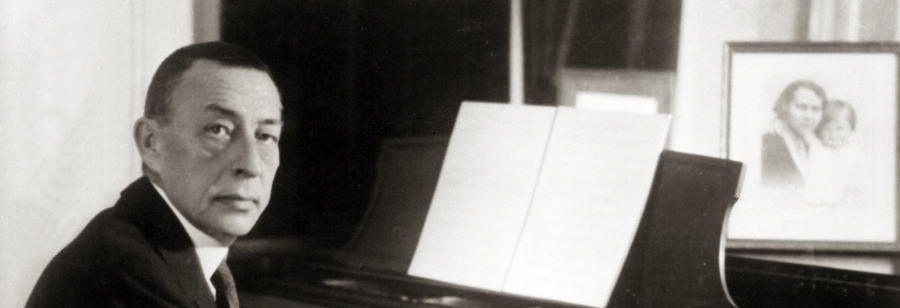
Rachmaninoff's Second Piano Sonata, Op. 36: Large Scale Narrative Consequences of Revision
Robert Carlson
Music - Piano Performance
A staple of the solo piano recital, Sergei Rachmaninoff’s Second Piano Sonata, op. 36, stands as one of the final romantic submissions to the art of the piano sonata. Rachmaninoff first published the sonata in 1913, and he returned to the piece in 1931 to revise it substantially, removing about five minutes from its performance time. Despite its compositional, emotional, and physical virtuosity, the work has received little analytic attention regarding the relationship between the two versions. This paper investigates the consequences of Rachmaninoff’s revisions by constructing a musical narrative for the sonata. The process illuminates structures within the piece that are central to its dramatic progression, and how revisions within certain sections can fundamentally transform the expressive relation between conflicting musical ideas.
Grayscale Thoughts: Reactions to Brown v. Board of Education
Haylee Orlowski
History
The 1954 Supreme Court case Brown v. Board of Education established that the segregation of public schools based on race violated the Equal Protection Clause of the Fourteenth Amendment. Across the United States, there was a spectrum of reactions to Brown. Responses ranged from optimism and celebration to anger and violence. This paper surveys the varied reception of Brown from politicians, parents, teachers, journalists, and other parties. It acknowledges the grayscale of opinions within and across demographic lines. The purpose of this paper is to recognize the complexity of a critical moment in the civil rights movement to prevent the oversimplification of American history.